DNS Issues : Pi-Hole being bypassed completely.
-
Hi Folks,
I have set up pfsense recently and struggling with the DNS setup. While I have been reading up a fair bit on the forums/blogs etc. but do presume that have missed out something due to inexperience with pfsense, and would appreciate some guidance.
My setup is:
- Dual WAN on pfsense
- LAN - 192.168.1.0
- 3 VLAN (IOT - 192.168.10.x, Guest - 192.168.30.x, Corelan - 192.168.50.x).
- Lan port is connected to a Unifi switch, which has the 3 APs and another switch connected.
- The VLANs are corrected passed through and DHCP is managed by pfsense. I have set up a pi-hole at 192.168.1.100 and configured the following.
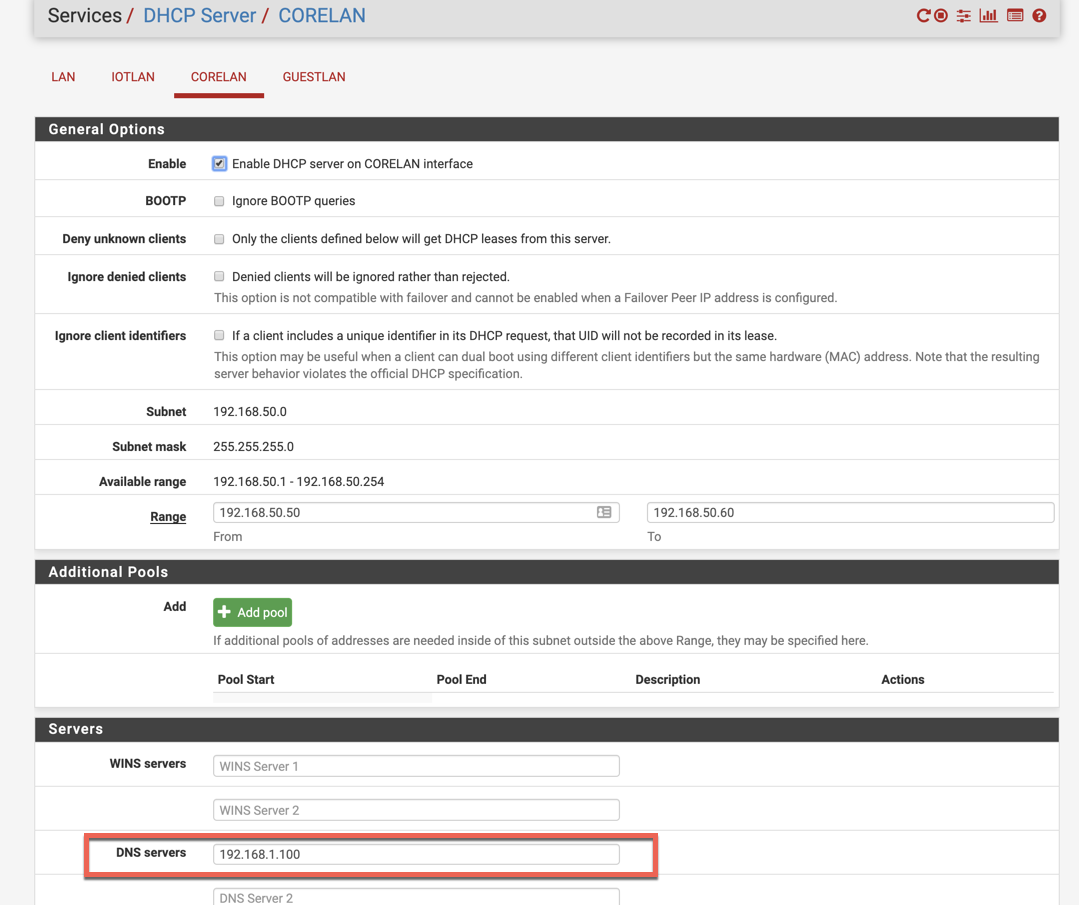
- For all VLAN DHCP setup, I have put the pi-hole IP as the DNS server.
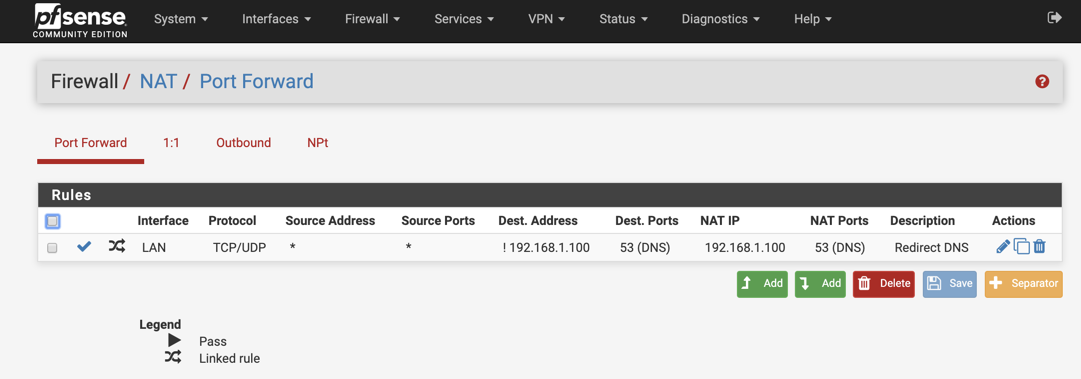
- Put a NAT entry to force all DNS queries to go to Pi-hole IP
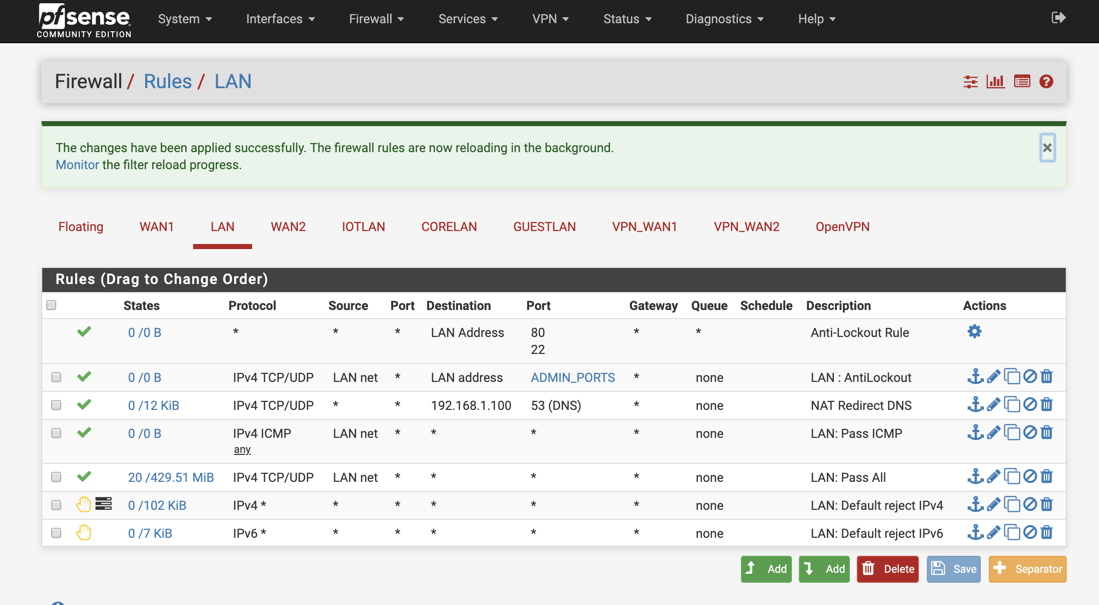
- The Lan firewall looks like this:
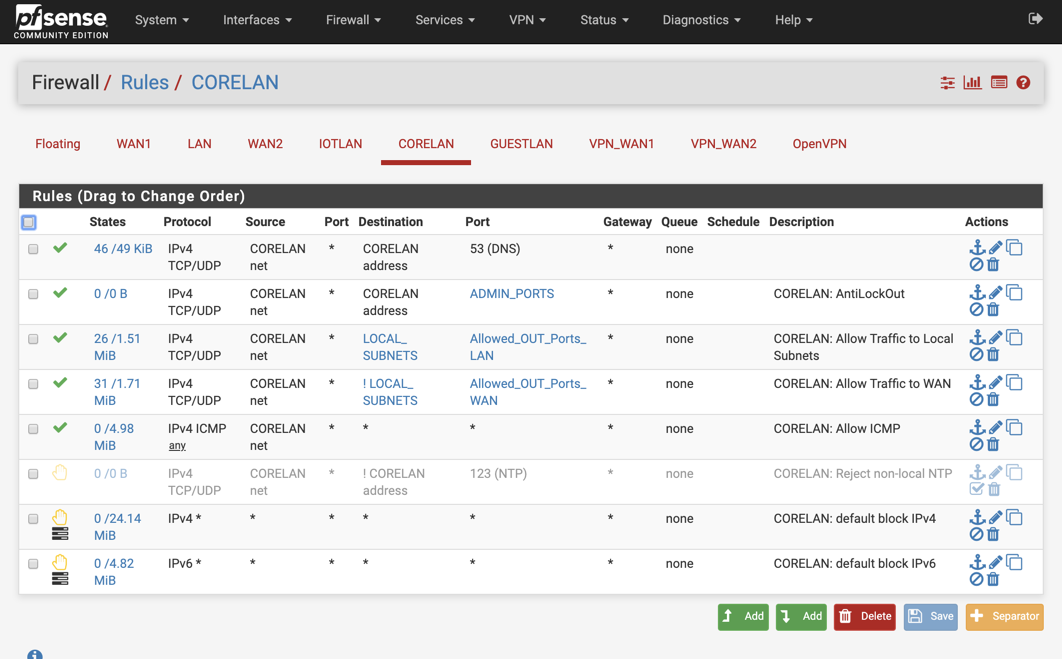
- VLAN firewall rules are these:
CORELAN:
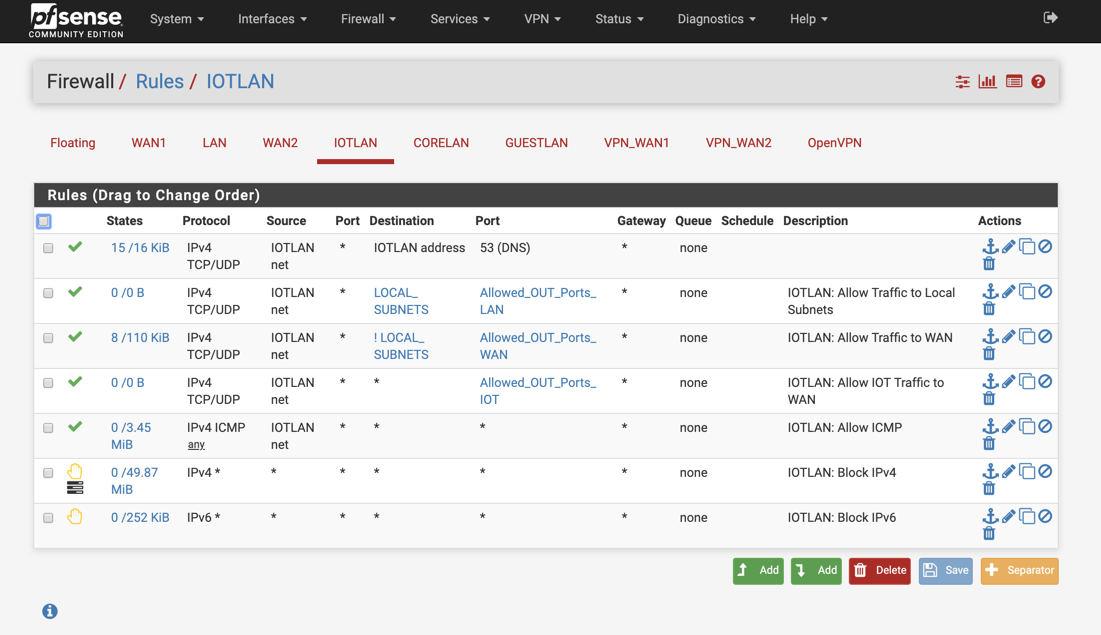
IOTLAN:
- DNS resolver is set up as follows. The NETWORK interfaces selected are IOTLAN, GUESTLAN, CORELAN and Localhost
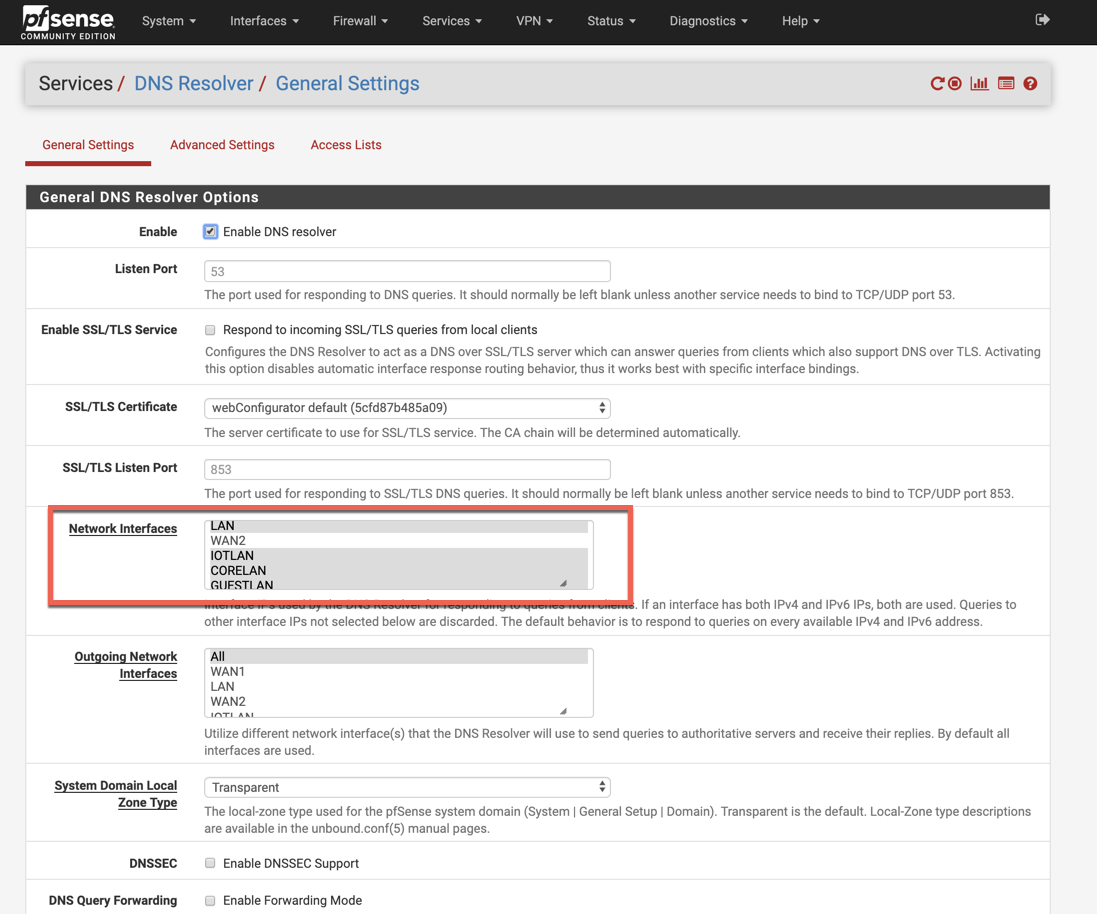
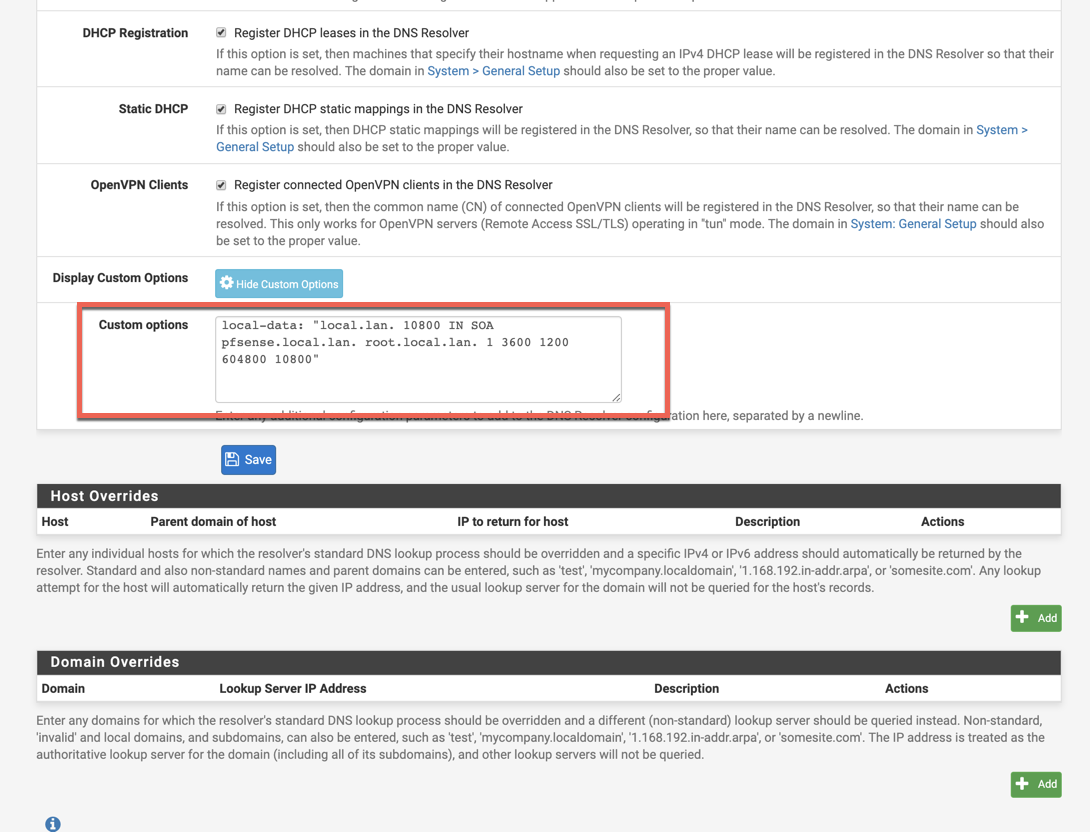
A few additional settings that I configured (nguvu.org)
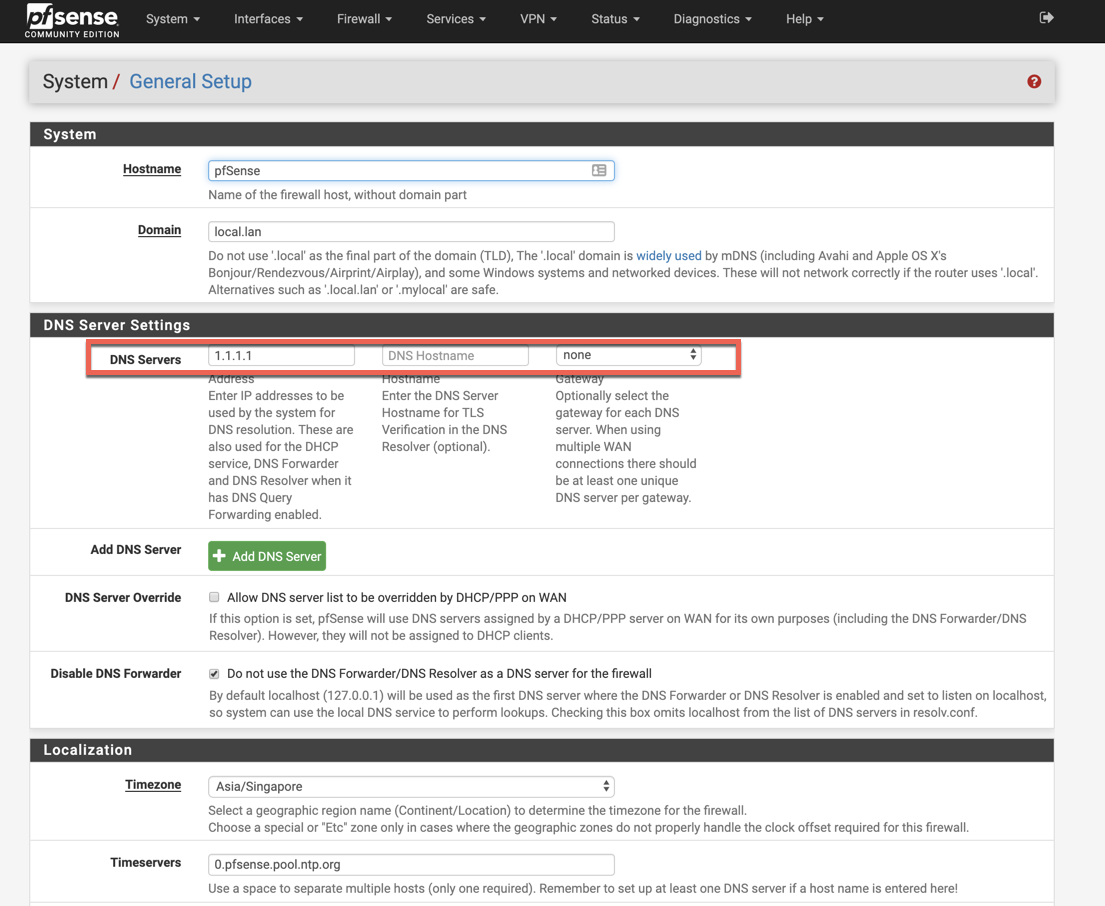
- Cloudflare is set up as the DNS in the 'General' screen.
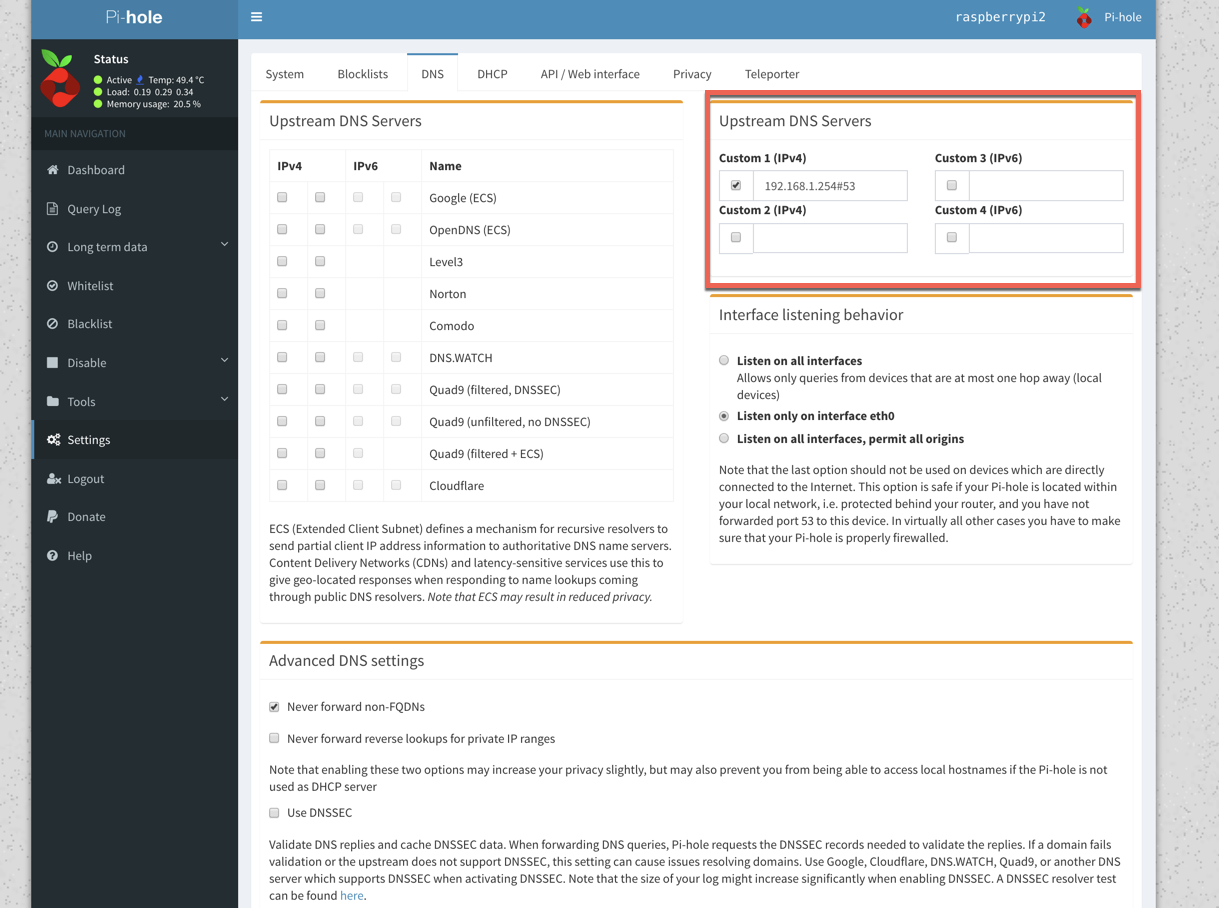
- Finally, in Pi-hole, the Upstream DNS server is set up as the pfsense box.
The challenge I am facing is
- Looking at the pi-hole dashboard, it seems only 2 clients are getting passed to this:
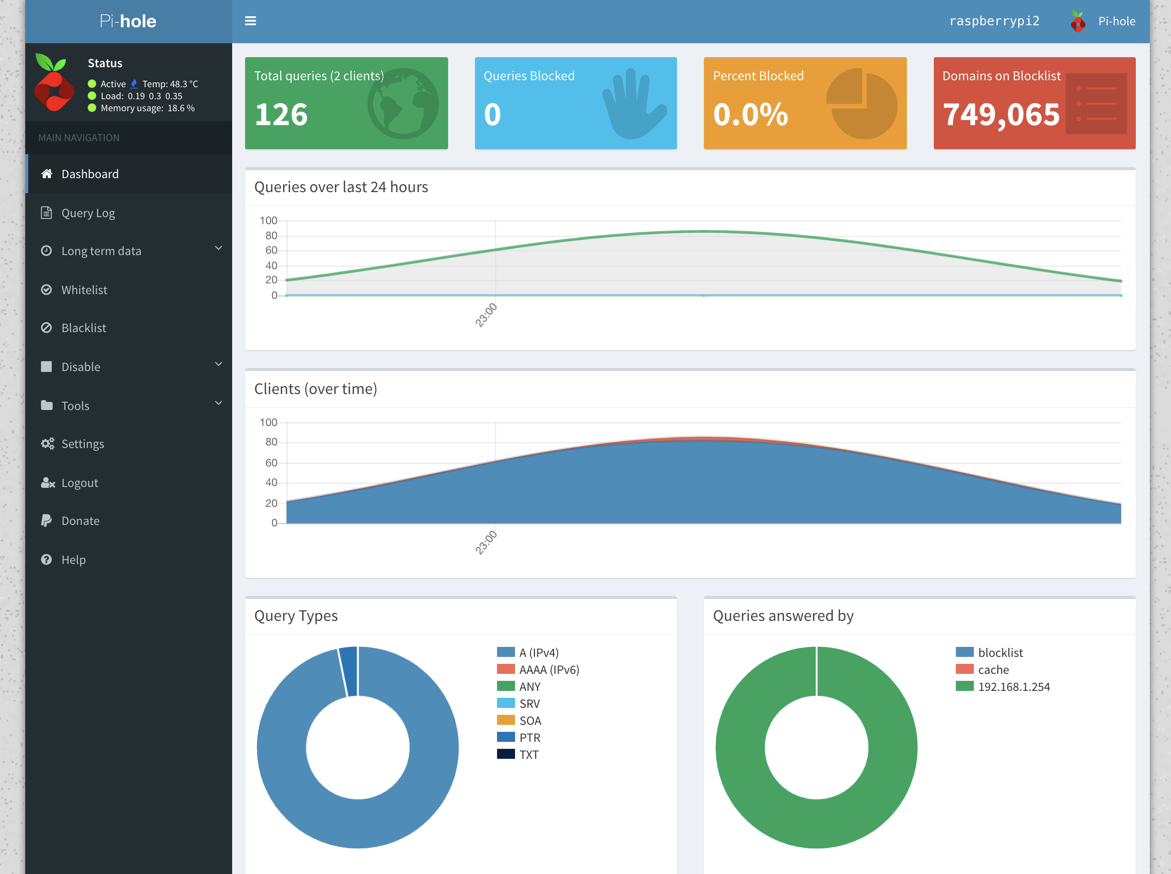
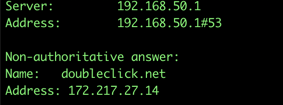
- If I try to do a nslookup for doubleclick.net, I am still getting an ip which means pi-hole is being completely bypassed.
I have been tinkering with this with different options, but just can't get this to work as expected. I would really appreciate if anyone can help point me in the right direction.
Many thanks in advance for any comments and feedback. :)
-
Are you running the
nslookupcommand from a Windows PC? If so, your problem is that PC has it's DNS server set to 192.168.50.1. That is not your Pi-Hole server, but instead appears to be the LAN interface of your pfSense box. Your firewall rules on the LAN interface are not redirecting all of your DNS traffic. The third rule in your screenshot of the LAN interface is only going to "catch" traffic that has a destination of 192.168.1.100, but your client (the one in yournslookupscreenshot) is not using 192.168.1.100 for its DNS server. It is using 192.168.50.1, so since the destination IP does not match neither does the rule. You need to get that DNS server setting on the client figured out and fixed. Your client will need to use 192.168.1.100, or else you need to change that LAN rule to SRC = any, SRC PORT = any, DST = any and DST PORT = 53. -
I am running this from a mac. 192.168.50.1 is the VLAN net address and since the mac is on this VLAN, I believe this should be correct? The NAT catcher is set on the LAN interface. Pi-hole is also set up on the LAN interface. The rule you mentioned on the LAN interface is a linked rule created by NAT.
I have been trying to test out various options (Resolver vs Forwarder) but so far not much success. Read another post which said that I need to put Pi-hole not on the LAN but in another VLAN for this to even work; That's the next thing I am about to test.
My goal from this is:
- All VLANs to send traffic to Pi-hole
- Pi-hole filters out the traffic for ad-servers
- Tracking which clients are sending out traffic to ad-services/blocked list more often
-
So I have managed to solve it...somewhat ;)
I disabled the resolver and used the forwarder instead. Put the pihole ip in the General->DNS settings. Removed the NAT.
Now, all queries seem to be going to pi-hole, and it appears to be blocking ad-servers. The only caveat now is that it shows the only client for pi-hole as the IP from pfsense and 127.0.0.1 :(
I am not sure if it's even possible at this point to get the individual IPs from all VLANs to show up in pihole.
. -
Hi @rajat - In general, the way I would recommend to set this up is:
Clients on LAN Subnets send DNS Request to Pi-Hole --> Pi-Hole checks its DNS cache, and if needed forwards the DNS request to pfFsense --> pfSense checks its DNS cache and if needed either resolves or forwards the DNS request (depending on if you have Unbound setup to run in resolver and forwarder mode).
In your case I see that you have Pi-Hole setup on your 192.168.100.x LAN subnet. Make sure you have added the necessary firewall rules to your other VLAN subnets to allow clients on those to send DNS requests to Pi-Hole, and then change the DHCP information on the VLAN subnets to make sure that Pi-Hole is assigned as the DNS server to clients. In Pi-Hole itself use the pfSense LAN IP as the upstream DNS server for Pi-Hole to talk to. Inside pfSense, decide if you want to run Unbound as a DNS Resolver or DNS Forwarder. If Resolver, there is no need to enter any additional DNS servers under General --> DNS Settings because pfSense will always resolve (i.e. talk to the DNS root servers first) if the DNS information is not available in the cache. If you are running Unbound in forwarding mode, you can enter your forwarding DNS servers in General --> DNS Settings.
Also, regarding NAT redirects: Right now I see that you have only have one NAT redirect rule on your LAN subnet. I don't think this will rule will do anything since any traffic originating on the LAN subnet 192.168.1.x bound for 192.168.1.100 (also LAN subnet) will not need to cross (i.e. talk to) the firewall. I think what you actually want is NAT redirect rules for each of your other VLAN subnets to ensure that if DNS traffic (originating from them) is not bound to Pi-Hole it gets automatically redirected to Pi-Hole.
Hope this helps.