NAT "same port" rule exception not working
-
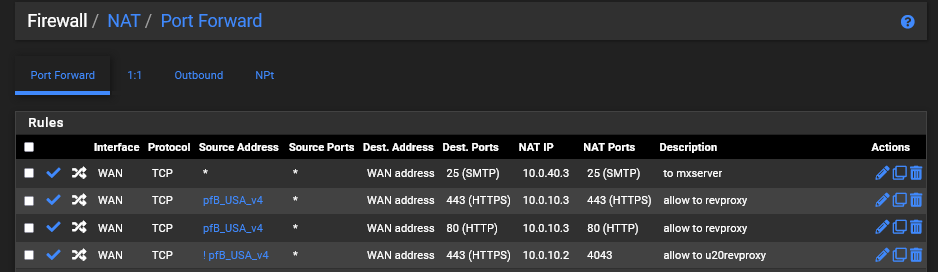
I have an alias for US ip addresses, NAT from port 80 to machine A port 80.
I am attempting the invert of the alias, NAT from port 80 to machine B port 80.Shouldn't this work? According to https://docs.netgate.com/pfsense/en/latest/nat/port-forwards.html it should.
I am getting this error:
The following input errors were detected: The destination port range overlaps with an existing entry.I should also add that the rule I'm trying to add existed before and was removed - I am trying to re-add it. The WAN firewall associated rule was removed before attempting to re-add.
I also have an existing pair of rules that are similar for port 443 (using alias and the invert), but those were added a while ago.
-
So you want to send US IPs to machine A on port 80, and you want all other IPs on the planet that are not UP IPs to machine B.
-
@johnpoz
More specifically, I already have been doing so, but cannot add back the rule.
It seems maybe an invert is no longer respected when determining the exception?
-
@gboone but if you send Alias X to IP X, wouldn't the inverse of Alias X just be any..
So you could do this couldn't you?
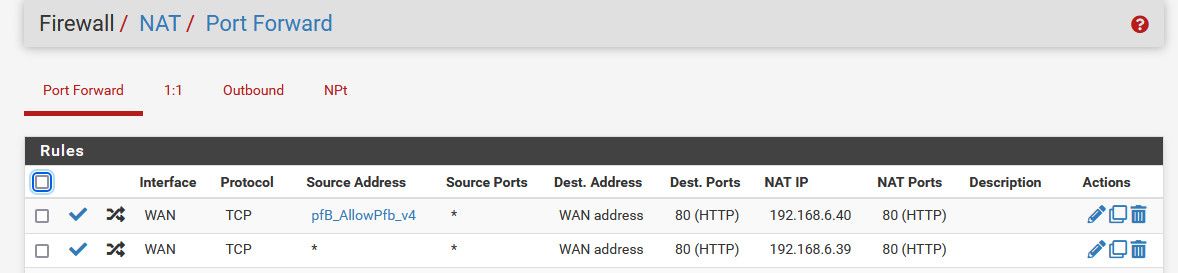
So with that order comes into play, if source comes in and is in the alias it would be sent to 6.40 in my example.
But if it was any other IP, ie NOT in my alias it would got to 6.39
-
@johnpoz Yes, that will work - thank you for the suggestion.
-
@gboone I get where your coming from with the ! for the source.. In theory you should think it would work.
Since the source would be different.. But could be problematic in parsing that rule - I have never setup such a rule in previous version. So not sure if something has changed.
Maybe better wording in the docs? To more clearly expand on the requirements of source or possible use of ! (inverse) in the source IP address.. I have read over the docs a few times - and I do not see it spelled out that doing a ! on the source IP or range/alias is viable way of doing it.
Could be just problematic in how pfsense checks the rules that they do not overlap. But the inverse or opposite of something specific like single IP or range of IPs or alias listing a bunch of IPs would be any.
-
It appears that "alias-on-given-port" is checked and the
invert matchof the same alias is ignored so it interprets the alias is used twice and throws the error.I ended up with a set up using pfBlocker that does work while using
invert matchon an alias, but it works within the constraint above.ListA - US
ListB - blocked geo
Technically, outside of these two would be the rest of "all".Setup:
ListA on port 80 -> machineA port 80 ListA on port 443 -> machineA port 443 !ListB on port 80 -> machineB port 80 !ListB on port 443 -> machineB port 443@johnpoz The documentation might need to include a note that
pfSense does not interpret the invert match of an alias to be a unique from the alias.The
invert matchon ListB above is ALL, like you suggested, but without ListB.Thanks again!