Multiwan and policy routing
-
Hello,
I'm newcomer in this forum, and not very familiar with pfsense. So thank to redirect me on other thread if there is some answer to my question in other thread.
I'm trying to configure multiwan solution on my existing virtual pfsense cluster (2.7, community edition)
My architecture:
- 7 internal interfaces
- 1 wan interco interface
- 1 site to site openvpn (client mode)
- both wan are reachable from same pfsense external interface (but next hop is different for each)
Currently, gateway group is configured with both wan (failover mode, tier1 for the first, and tier2 for the backup), and IP monitor associated to static routing is working. I'm able to see failover in gateway status.
This gateway group is also used as default gateway for my pfsense cluster.
As I can see, default route is automatically changed in routing table when there is an issue with the primary wan.
My issue is that traffic coming from lan continue to go to the failed WAN. In some documentation, I can see we need to configure firewall rule to specify gateway group. Is it really mandatory for failover architecture? Not only for loadballancing? As this quite complex to maintain routing table and policy routing config aligned (with OpenVPN routing too)
Thank you for your feedback.
-
@hyperman35 said in Multiwan and policy routing:
As I can see, default route is automatically changed in routing table when there is an issue with the primary wan.
My issue is that traffic coming from lan continue to go to the failed WAN.
I don't expect that newly initiated upstream traffic goes out to another than the default gateway.
However, this may concern already existing (long-term) connections though.As a workaround you can flush the states, when a gateway goes down by checking System > Advanced > Miscellaneous > State Killing on Gateway Failure.
-
Hello,
Thank you for answering.
I already activated this option, with no change.
Question : so my configuration, without changed on my policy should work ?
Thank you
-
Hello,
Is someone has some ideas for my issue?
Thank you !
-
Hello,
I made a test, by trying to configure the secondary WAN in a different network interface/network. It seem that in this case routing is working as expected.
In case of both nominal, and secondary WAN are in same interco network => only default route is considered (including a simple traceroute from pfsense itself), and monitors are not working... I think this is same issue when gateway failover occure => network traffic continue to follow the previous route (normal default route)...
Did someone encounter some kind of issue with multiple next hop routing issue when in same subnet/interface ?
Thank you.
-
Hello,
I made some tests today.
I modified my architecture : now both WAN gateways are on different VLAN. And all seem working as expected...
So I think there is a "bug" (exept if this is the expected beahviour, but I didn't see anything about it) with routing, when both WAN GW are reachable through same PFSENSE logical interface (same interco VLAN for both GW).
Does someone encounter same issue ?
Thank you.
-
@hyperman35 That is no bug but outbound NAT will not work automagically if I remember correct. If you can, separate the gateways to different interfaces.
-
@Bob-Dig thank you for your answer.
Of course, it what I explain on my previous message (sorry if it was not clear). Now both Internet access are availble through 2 differents interface, and all is working as expeded.
What I call a bug, is more, related to the routing issue (no NAT relation, as the issue is also visible for packet generated by the FW itself). What seem a bug is more related to routing issue , when using 2 routes, with 2 different next hop on same vlan/interface (issue also exist for simple static routing). This is quite simple to reproduce : try to add 2 static route for 2 specific hosts, with 2 differents nexthop. When using traceroute command, for each IP used for static route, routing is still going to the bad route for one of them...
-
@hyperman35 Maybe you have not setup your gateways right is what I guess.
Take a look here, all are on the same interface, works like a charm.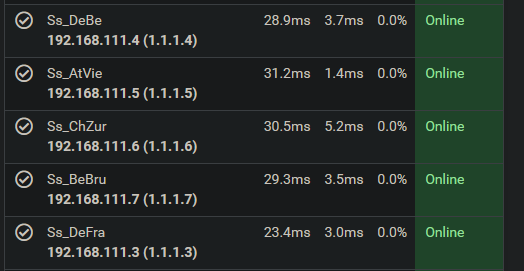
-
Ok so it was exactly what tried to do with no luck...
But ok let work with my new architecture, with 2 differents vlan => this is ok for me.
Thank you for your help !
-
@hyperman35 Now I do remember what you shouldn't do, maybe this helps. Don't put any upstream gateway on the interface tab, it has to be None there for multiple gateways.