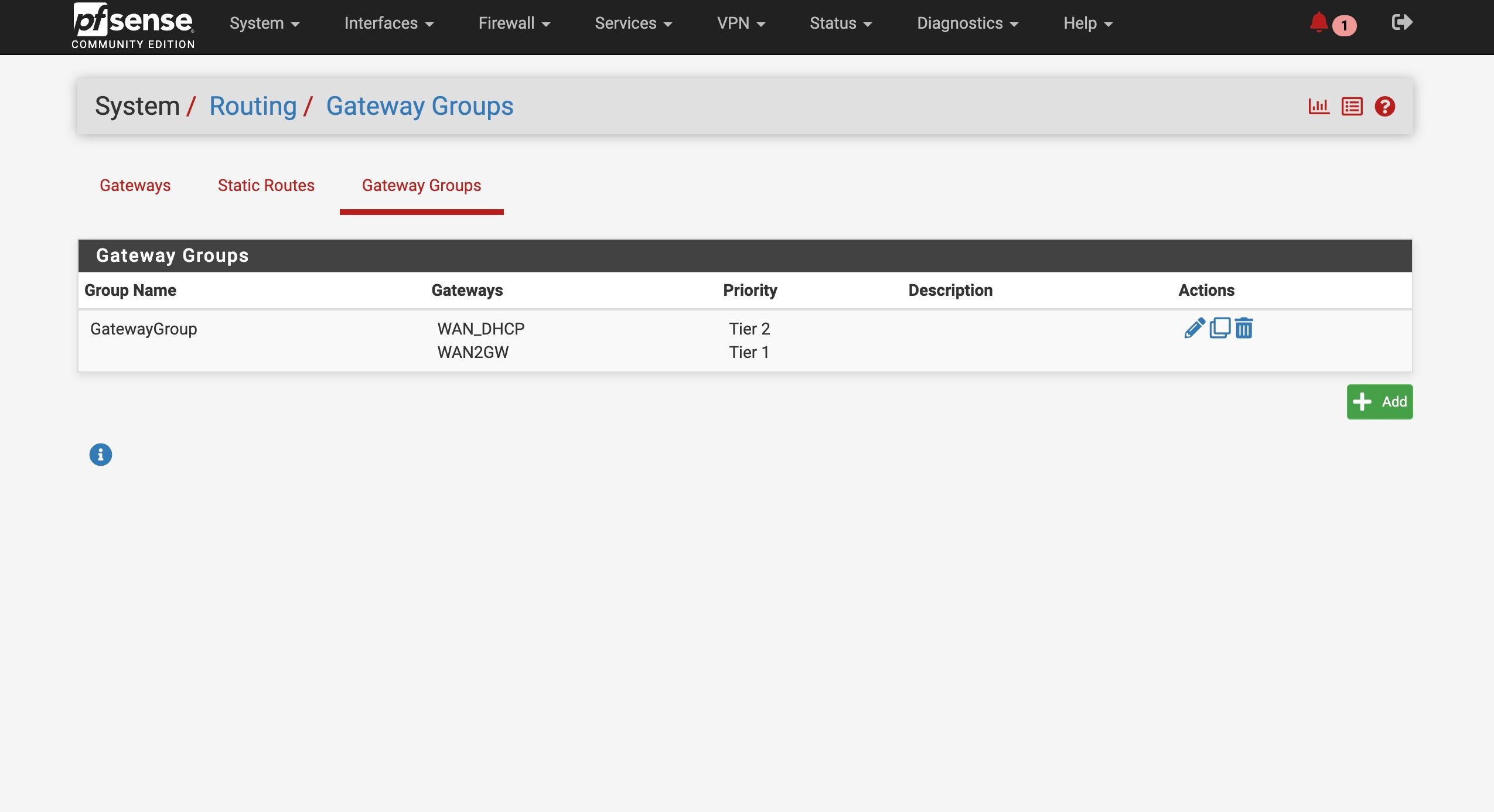
ATT Internet AIr
-
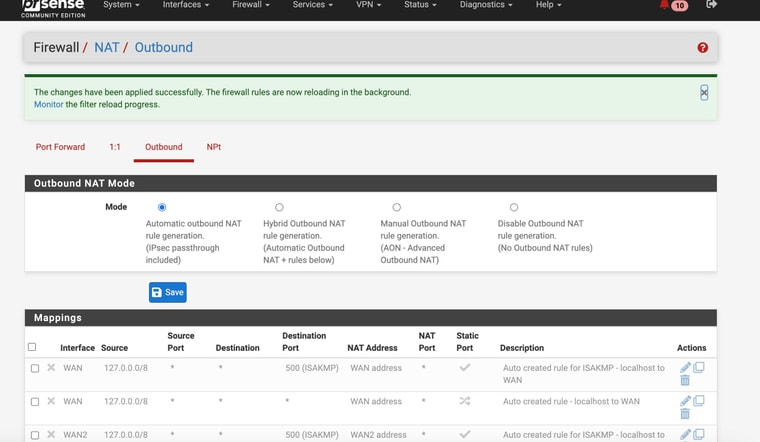
@stephenw10 Oddly I changed back to "Auto Mode" for Outbound NAT and it still worked
-
Hmm, interesting! That still using 192.168.2.1 to access it? It seems like the Nighthawk has a route to the public IP then. In which case that's no problem.
-
@stephenw10 yes still using 192.168.2.1
-
Should be fine then. Some modems do not require a NAT rules and can use the public IP on WAN to reply to.
-
@stephenw10
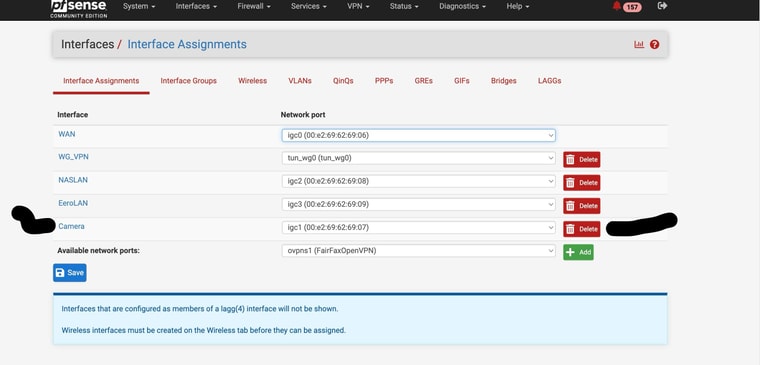
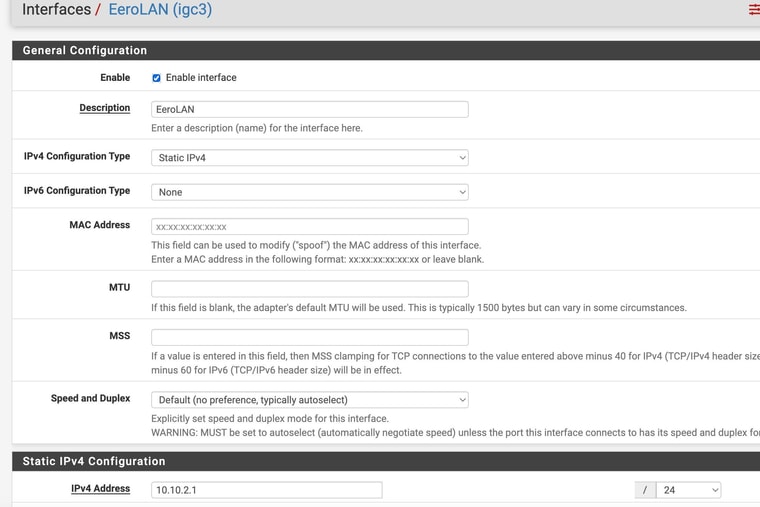
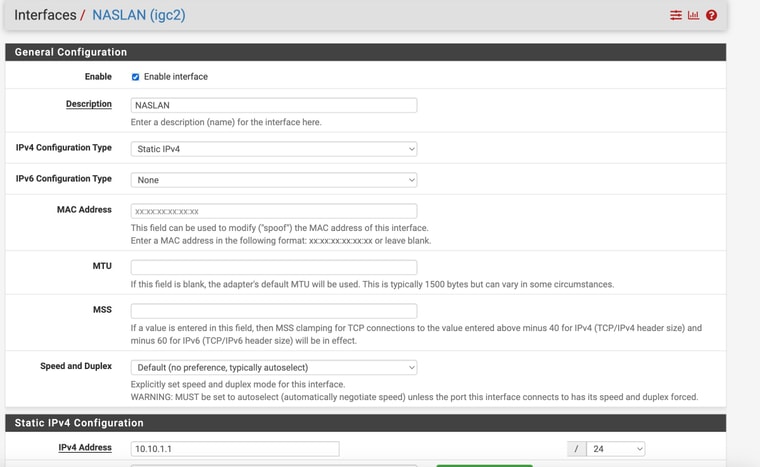
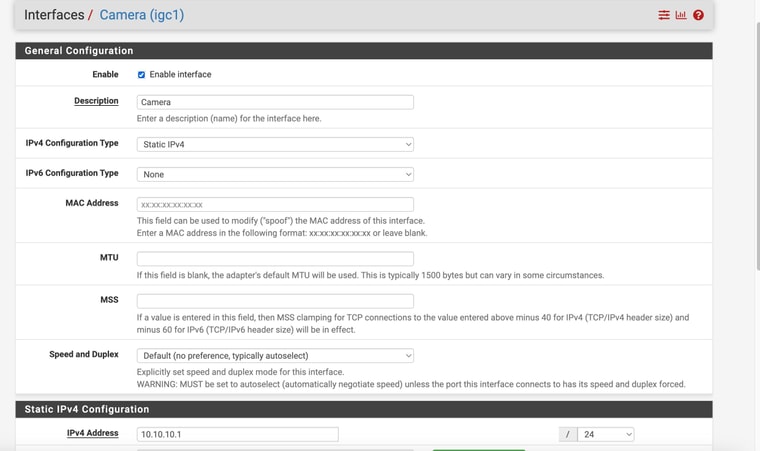
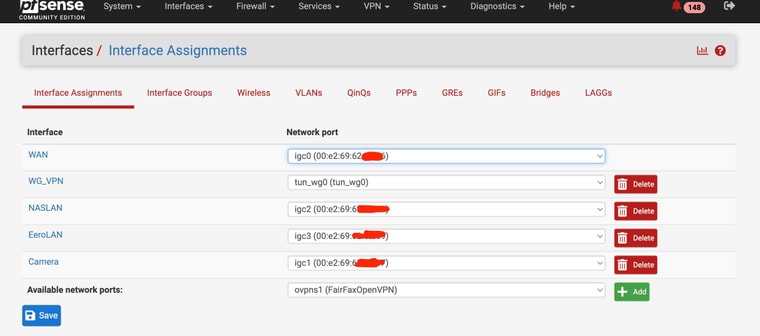
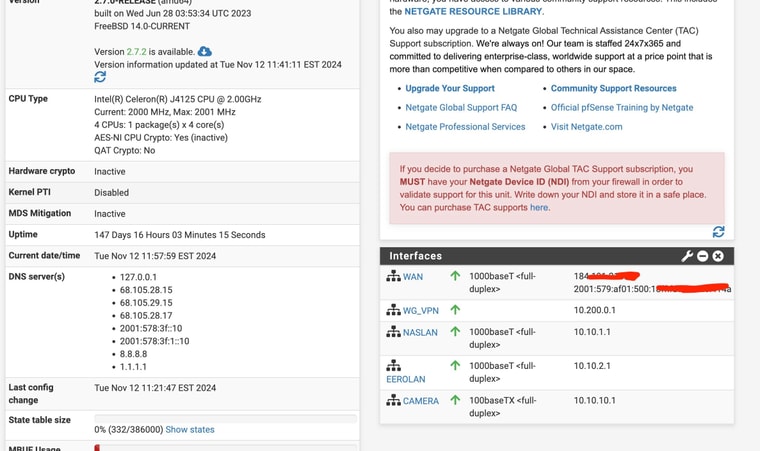
Now that I have survived that ordeal , lol (with you help) - I have to replicate the process at our second location.My pfsense device at that location only has 4 ethernet ports just like the one I have at location 1 - however, at location 2, I have all 4 ports used as per the pics. 2 are for security camera ports, one for and eero wifi and 1 for my NAS.
I have them on differnt networks.
What would be the best way to salvage my current equipment and still setup a failover internet (second WAN)? since my ports are filled
-
-
Add a VLAN capable switch and use it to separate some ports is what I would do there.
It might be possible to use the eero device to do that if it supports VLANs.
I assume you need to be able to filter between those three interal interfaces with different rules for each?
-
@stephenw10
Haven’t used VLAN for this but wanted to make sure == I could buy this $20 switch
Change maybe my pFsense Camera interface to a VLAN parent interface?
Connect to one of the switch ports
And then have one port assigned as the Camera VLAN
And then could I assign another VLAN port as the WAN2 connection for my ATT failover ??Would that work? Can a VLAN port be used as a WAN connection
-
Yes exactly like that. The ports on the switch can be configured as access ports on different VLANs. The link to pfSense can carry all the VLANs. pfSense treats the VLANs as separate interfaces. And yes it can be a WAN, or any interface type.
-
@stephenw10 Perfect. thanks
-
Currently at my primary business location I have cameras on the same subnet as other devices - like the NAS, etc. My second business location as you might remember from above discussion has cameras on a seperate subnet.
Ideally I would like to keep acessing my cameras with the Synology Surveillance station which is within my network. However an alternative is to use the camera manufacturer software - but that requires a port forward., to be accessed externally.Is there a way to open several LAN IP addresses to a specific port - or even entire subnet to a particular port ? Or do a I need to change each individual camera to a non-default individual port?
Just trying to be the safest possible if I end up opening another port externally
-
Hmm, well I would avoid opening port forwards to each camera like that if at all possible. Especially if they are on the same subnet as other local resources.
To do it you would need to use a different external port for each camera and forward that to the internal camera IP. That way they can all be forwarded from the same external IP. But don't do that!
-
@stephenw10
OK. Maybe I better just keep doing the VPN connection and use of surveillance station which is part of the Symbology NAS
If that is the case and a VPN is used for external access with no open external ports is there really a strong security reason to have the cameras on a different subnet? -
Because any IoT device like that is always going to be a target for exploits. They usually only see updates for limited time (if you're lucky!). And if they are on the same subnet as other things then if a camera is compromised anything running on it will be able to directly connect. Or at least try to.
-
@stephenw10
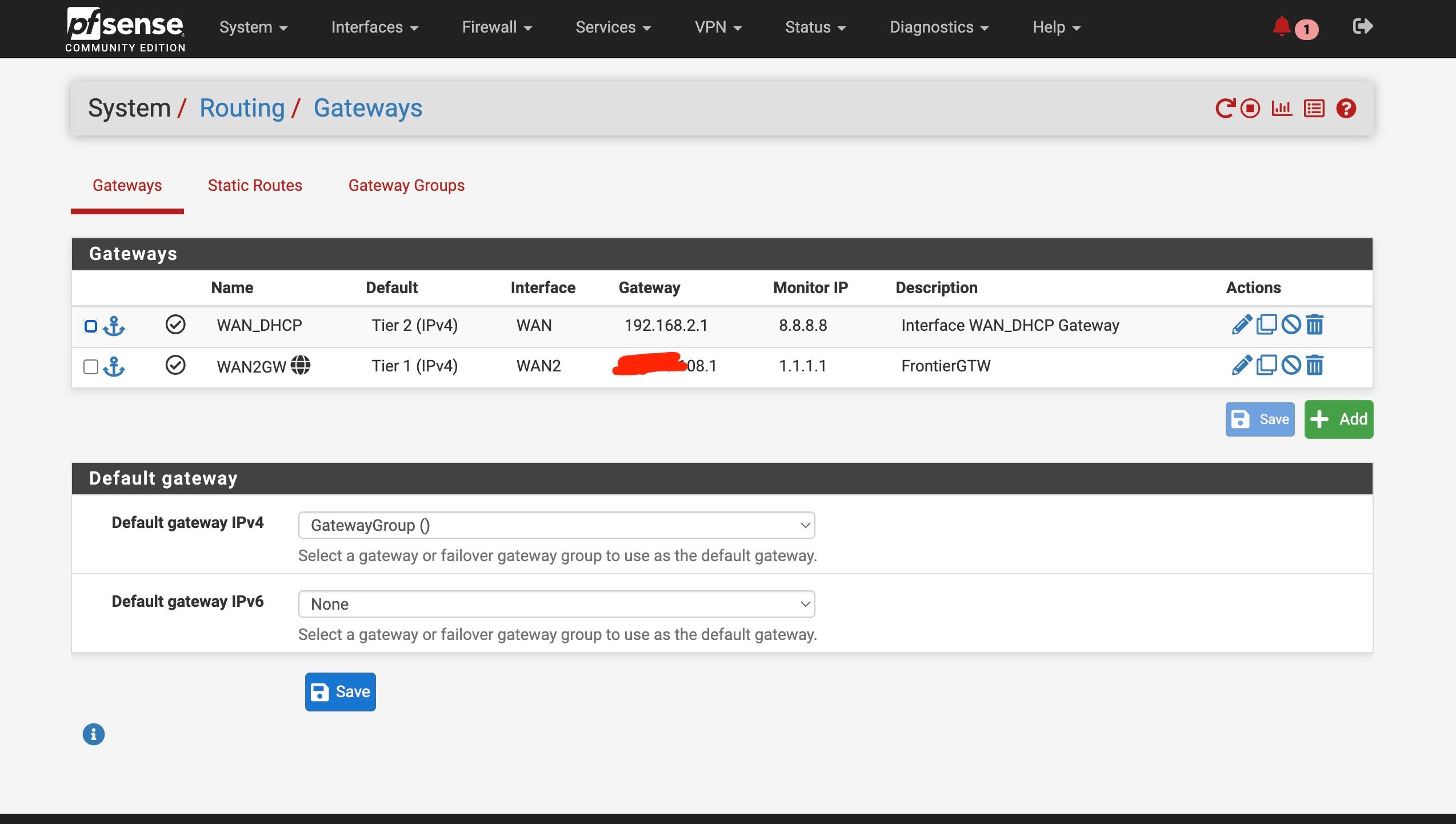
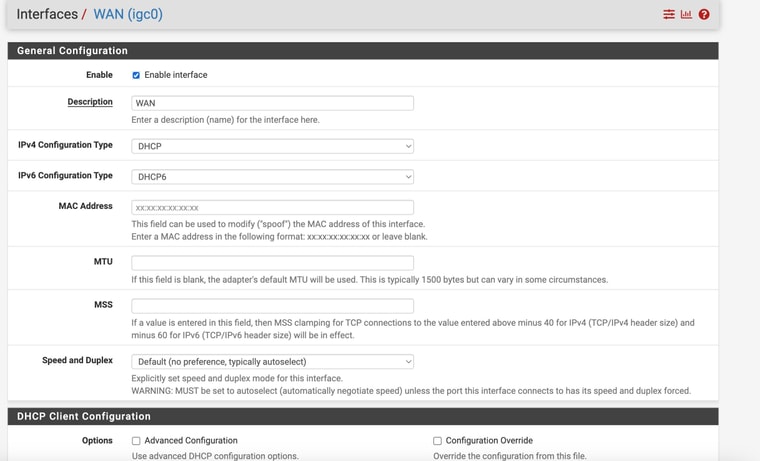
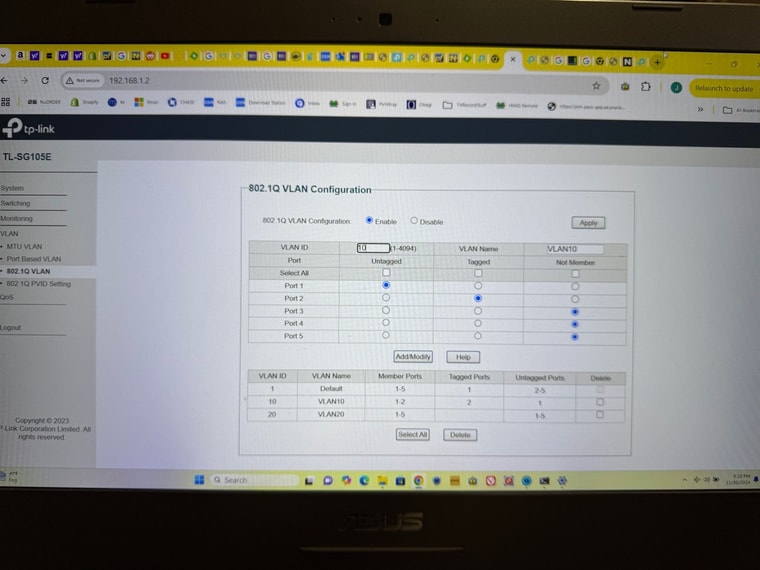
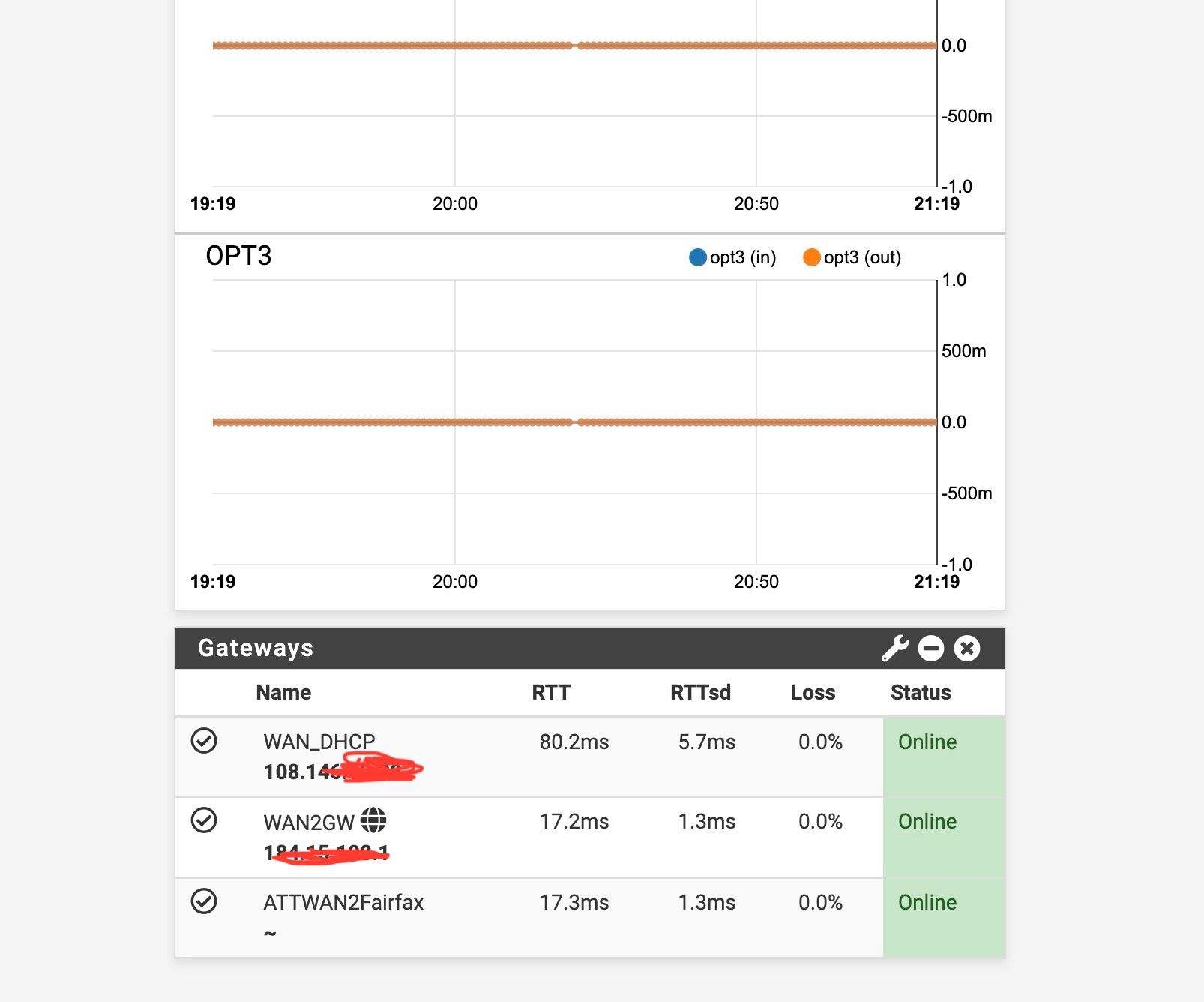
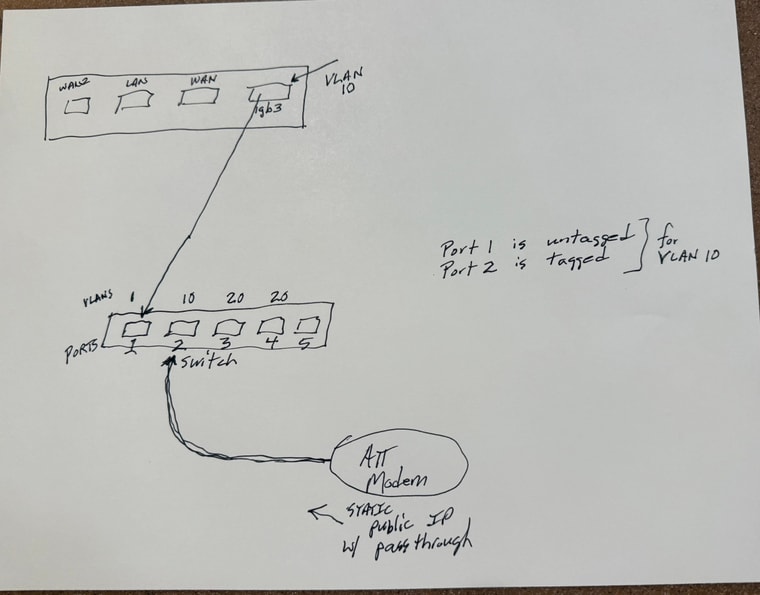
Lost again - hopefully you will have time / energy to help:As I mentioned I am trying to setup the addnl WAN ATT modem on my second store system. I mentioned that my pfsense device is a 4 port device with all 4 ports utilized. We talked about a VLAN capable switch - I purchased a TP-Link TL-SG105E
I am 5hrs off site so I am trying to get up to speed to manage remotely by trying the switch on my current system.So I have created a VLAN with a tag of 10 on interface igb3.
I have TRIED to setup my TP-Link switch (in preparation for the setup that I am currently offsite from) with port 1 being the "trunk" that a cable will be connected to igb3 (on the pfsense).
Port 1 is untagged for VLAN ID 10 and is identified as a "1" in PVID Settings
Port 2 is tagged for for VLAN ID 10 and is identified as "10" in PVID settings
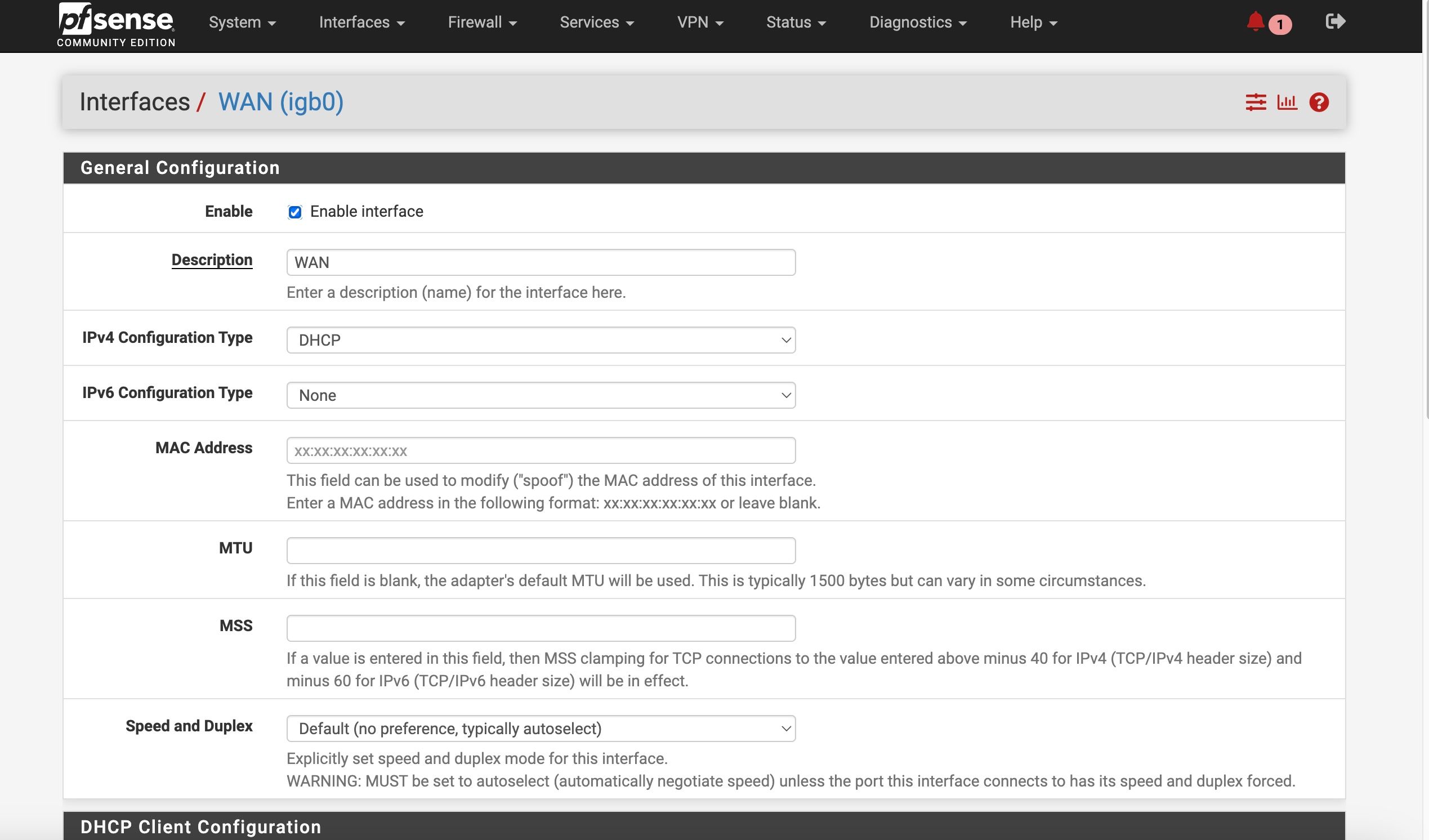
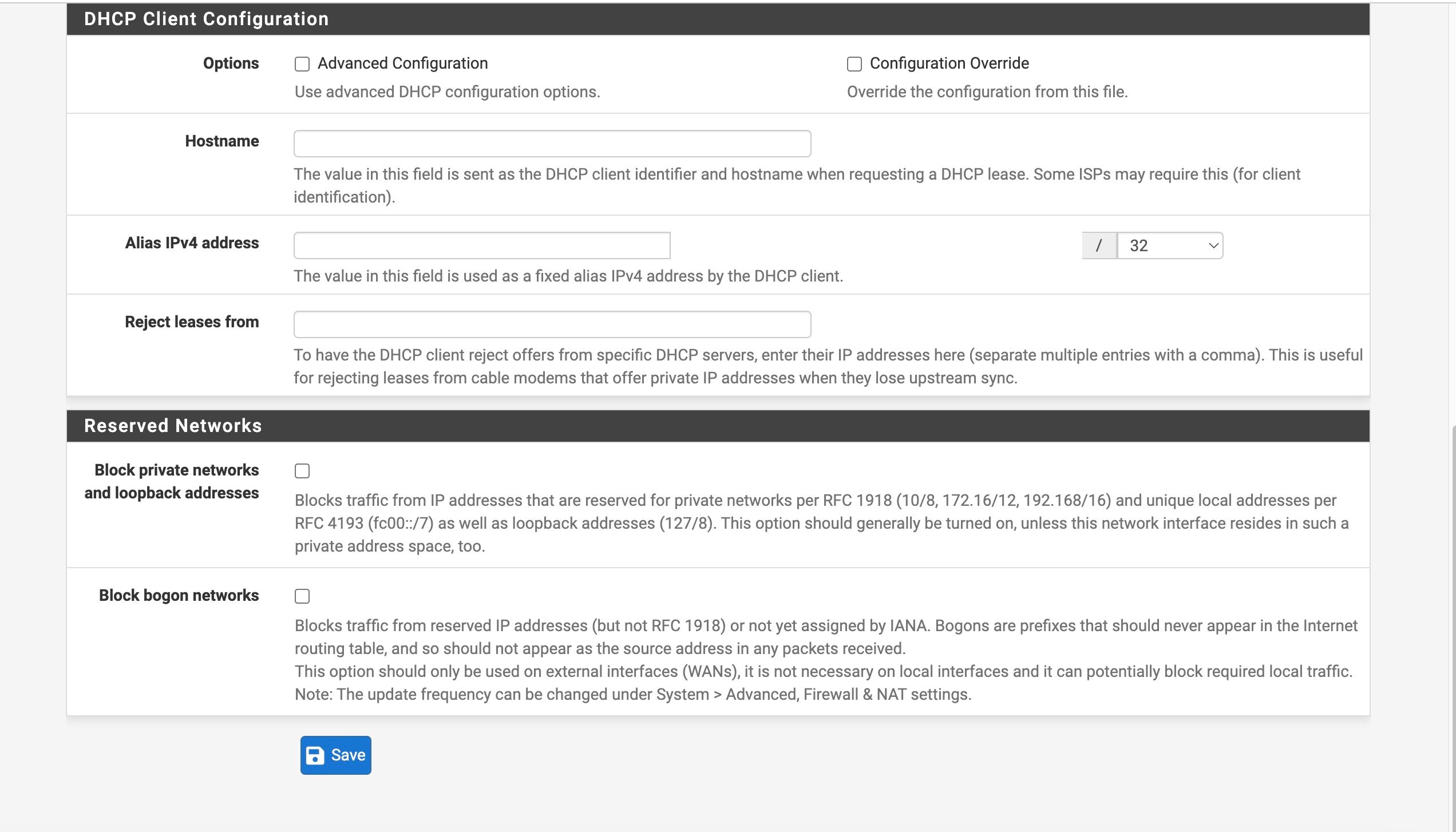
(Port 3 and 4 if needed will be VLAN ID 20 for the additional LAN cable that is needed for the Camera segment of my network)The current trouble I am having is that my identical ATT device, when connected to port 2 of the switch, is not passing through the IP address when I created or setup the interface as DHCP -- the other ATT device when connected directly to one of the pfsense interfaces pushed through ATT static publc IP address. And if I try to set the IP address manually it doesn't behave correctly- says offline
I think I must be setting the VLANs and the switch incorrectly (tags vs untagged, etc). Would you expect a device (in this case the ATT modem) to behave the same way when connected via VLAN and the switch compared to connecting directly to the pfsense physical port? I thought that was the whole purpose
Do you see any glaring errors in my setup?
-
@ahole4sure said in ATT Internet AIr:
The current trouble I am having is that my identical ATT device, when connected to port 2 of the switch, is not passing through the IP address when I created or setup the interface as DHCP -- the other ATT device when connected directly to one of the pfsense interfaces pushed through ATT static publc IP address. And if I try to set the IP address manually it doesn't behave correctly- says offline
Looking at your picture, I see WAN, LAN and WAN2. So what is it that you are trying to do with the ATT modem now, connecting it to the fourth port? Are you trying to add a third WAN?
I don't understand the direction... If your VLAN is set up on pfsense, you make port 1 a TRUNK port as you said, but that means TAGGED 10. And the ports for any devices that should only belong to VLAN 10 need to be untagged and only members of VLAN 10. Currently all ports are also members of VLAN 1...
If you are trying to get an IP on port 4 on pfsense (igb3) from the ATT modem, you can simply make both ports 1 and 2 VLAN 10 UNTAGGED on the switch. Remove them from any other VLAN memberships.
This way you have created a "switch within the switch", where port 1 and 2 are connected but separate from the other ports. Pfsense doesn't need to know of any VLAN on igb3 for this to work... -
Yup that^. Port 1 should be tagged for VLAN 10 because it has to pass tragged traffic to pfSense. Port 2 should be untagged for VLAN 10 and have the PVID set as 10 (as it is).
-
Thanks for input
Yes @Gblenn my apologies for confusion -- the weird setup is because it is just for testing (and being done on the system that is currently available to me - and yes in this test, adding a third WAN)
Once I get a confirmation that I can set this up and it will function properly then the real situation is depicted in the attached.Basically the real setup needs to have proper switch setup for the current "Camera" interface to be split so that the newly added switch can accept 2 ports (one for the newly added ATT modem and the original camera network) - see diagram.
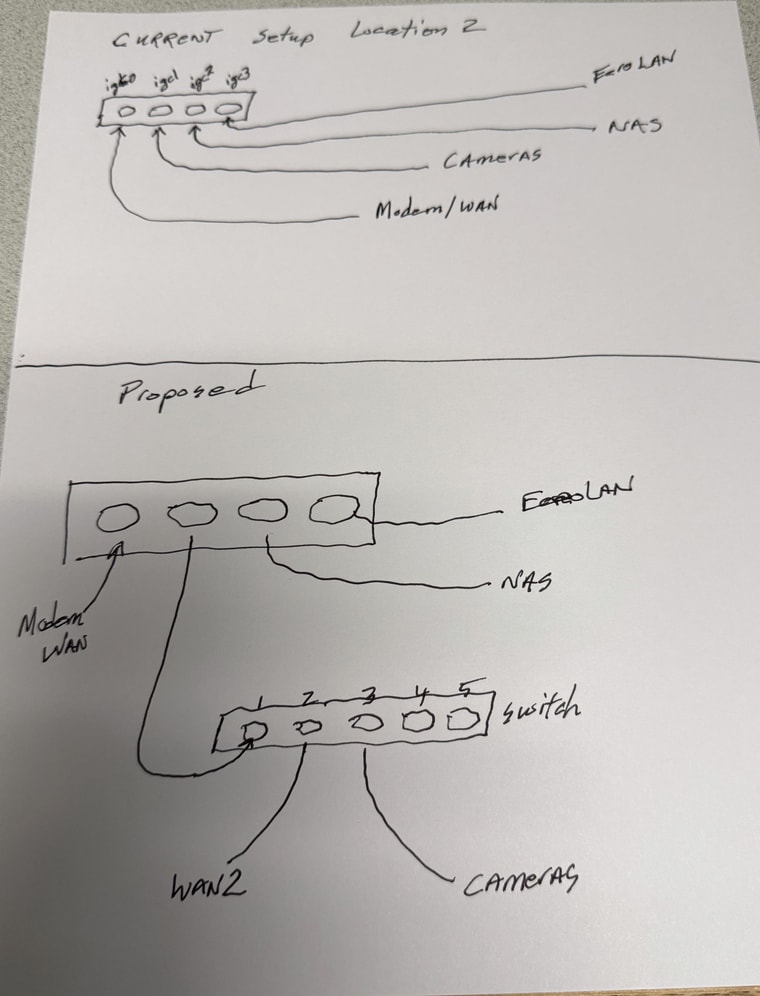
The reason for the change is to add a failover internet scource but i have no availabe addnl ports on the pfsense box.
In this real case scenario I will have the camera VLAN as ID 20So any input on how I would setup the switch (membership, tagging etc) would be appreaciated !! I have a feeling when the light goes off it is going to be easier -- but initially setting up the switch and VLANs is not as intuitive as I had thought. ugh
-
As discussed you can use just one VLAN there and have untagged traffic for the other subnet. But I would avoid that and use two VLANs instead because it avoid a bad config putting traffic onto the wrong interface.
So I would add VLANs 10 and 20. Make port 1 tagged for both those.
Make port 2 untagged for VLAN 10 with PVID 10.
Make port 3 untagged for VLAN 20 with PVID 20.
-
Another question for the situation (and in general)
So in general when you make an interface assignment and connection to VLANs (like in my case) do you need to delete the physical connection assignment - ie Camera in theis case?
And then of course make the new assignments to whatever VLANs you are connecting there?Is there an easy way to transfer or use all of the current network settings (rules, routing etc) for the Camera network - or in my case do I just leave it as it is and traffice gets passed to port 3 just like it is coming to igc3 natively currently?