@rtw915 said in Snort custom variables:
@bmeeks said in Snort custom variables:
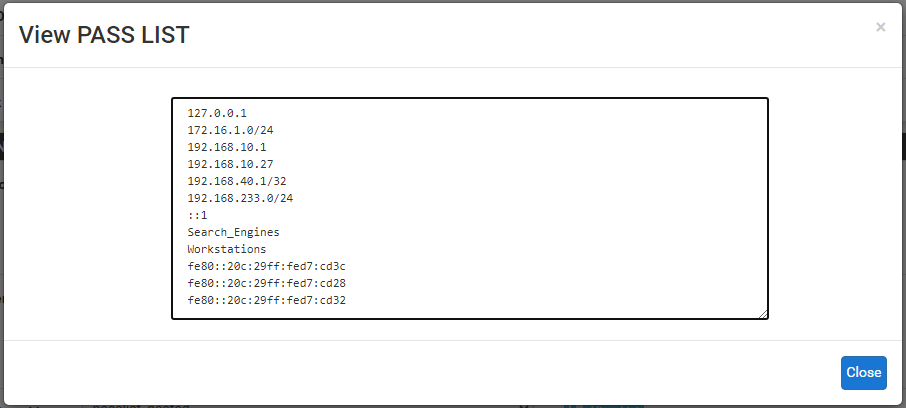
You don't really need a Pass List with Inline Mode because you are not blocking an IP. You are just dropping individual packets when they match.
Over dinner I read through the snort inline thread and the adjustability of the rules so you can alert or block is huge. I can see so much value with running snort inline. However, I was pretty bummed out to see the limitations with lag and VLANS. I use both of those technologies when architecting highly available networks.
It got me thinking though, that the inline mode and the custom output plugin you wrote really provide two different strategies. Along with some of the other posts you've written I'm starting to question my IPS approach.
My approach has been to identify bad actors in any way possible so that they can be blocked to prevent future harm. So say for example a bad actor is attacking using an ActiveX vulnerability and even though our environment doesn't use ActiveX I still have those rules enabled. This way if the same attacker moves on to use a SQL injection attack they are already blocked, as they don't become unblocked in my case for an extended period of time. At which point I'm hoping they'll just move on.
The limitation with VLANs and LAGG is due to the way the netmap kernel device is plumbed within FreeBSD. It's not a Snort limitation. The netmap idea had great promise when it was introduced a few years ago into FreeBSD and Linux, but some of the grand plans have not taken shape. Thus the various limitations of the technology. You can read up on netmap via Google searches.
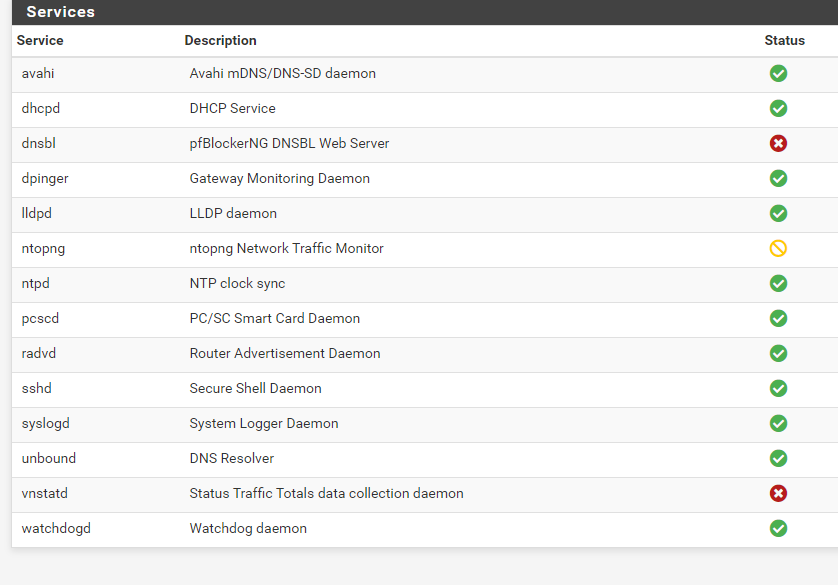
As for IDS/IPS strategy, there are as many opinions on what is "right" as there are IDS admins. But generally I favor keeping the workload on my firewall as light as possible while still affording protection. The reality is that almost any firewall today is pretty darn secure. This is especially true if you limit the amount of third-party stuff (such as packages) that you install on it. Remember each installed package brings in a bunch of shared libraries that may, in turn, bring in still more shared libraries. And any of these libraries can harbor vulnerabilities. So the fewer packages, the better.
As for blocking, as I stated, I'm not a fan of putting in specific blocks for the world. Put in Pass rules for explicitly what you want to come in (unsolicited), and then let the default deny rule take care of everything else. If you don't trust your firewall to be secure on its own and by default, why are you using it? (Rhetorical question, not an accusation ... ).
For IDS/IPS, run the rules that protect the exposures you have. Don't waste CPU and RAM resources on rules that protect against threats you are not vulnerable to. Spend your time and effort keeping your internal machines patched with the latest security hotfixes. That is 99% of cyber security right there! And it's much more effective than running every pfBlockerNG IP list or Snort rule in existence.