@jogovogo said in No Internet access with VLAN via OPT1:
My first surprise is that I'm now on the firewall, but why?
The web server that serves the pfSense GUI runs on all assigned interfaces.
When you installed pfSense, there was a pass rule for incoming traffic on the initial LAN interface : it accepts all traffic.
When you add more LAN type interfaces, the ones called OPTx, there will be no inital rules, so you can't access anything.
DHCP will work as pfSense will add hidden DHCP (UDP port 67 and 68) rules, but nothing else (no http https dns icmp etc etc etc etc).
When you add a pas rules for TCP, UDP, etc, things "start to work".
When you use addresses like this :
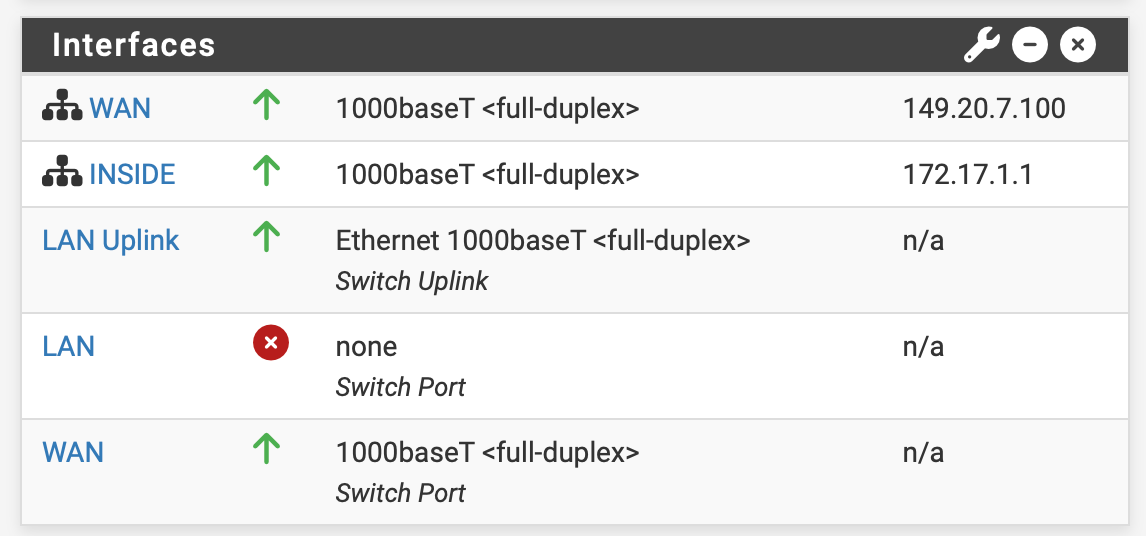
[image: 1758697659291-89b7f27a-e729-4579-81c1-cb12989a7d3f-image.png]
you use IP addresses.
So, even is DNS is not working, then that won't be an issue.
Your browser doesn't need to use use DNS (for translating host names to IP addresses) as you already gave an IP. It can contact the device 192.168.151.1 right away.
You've allowed TCP IPv4 traffic to port 477, which is apparently your changed your pfSense https web GUI interface port.
@jogovogo said in No Internet access with VLAN via OPT1:
The issue has been resolved, simply, by restarting the DNS resolver.
Euh ......
As you've changed lost of things at the same moment, it's hard to tell why dns (== the resolver) didn't work initially.
Normally, when you add an new interface like your OPT1 interface, system processes like DNS (the resolver) gets restarted.
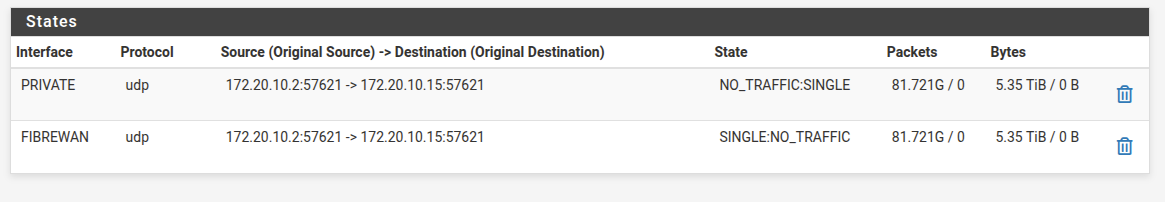
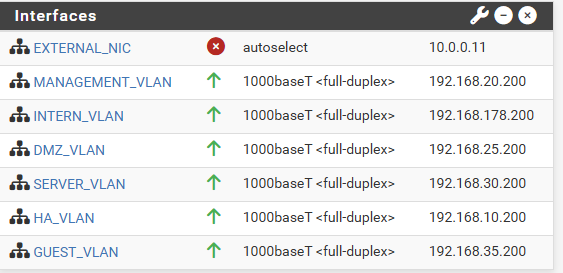
The resolver will listen to All Interfaces :
[image: 1758698045123-e07276c8-27b7-4a13-b999-ca154f396adf-image.png]
by default so it would work right away on the new OPT interface.
Again, you still have to add a firewall rule to allow DNS traffic to reach the pfSense DNS port 53 of course.